The New Nitrokey 3 With NFC, USB-C, Rust, Common Criteria EAL 6+

The new Nitrokey 3 is the best Nitrokey we have ever developed. It offers NFC, USB-C and USB-A Mini (optional) for the first time. The Nitrokey 3 combines the features of previous Nitrokey models: FIDO2, one-time passwords, OpenPGP smart card, Curve25519, password manager, Common Criteria EAL 6+ certified secure element, firmware updates. This reliably protects your accounts against phishing and password theft, and encrypts your communications and data. With strong hardware encryption, trustworthy thanks to open source, quality made in Germany.
Use Cases
For private and corporate use - protection against mass surveillance and hackers
- Passwordless login: Forget your password to log in to Microsoft services (e.g. Office 365) and Nextcloud and use Nitrokey for passwordless login instead.
- Protect online accounts using two-factor authentication (2FA): Nitrokey is your key to secure login to websites (e.g. Google, Facebook; overview at www.dongleauth.com). Using FIDO2, FIDO U2F, or one-time passwords (OTP), your accounts remain secure even if your password is stolen.
- Phishing protection: When using FIDO, the respective domain is automatically checked and users are effectively protected against phishing attacks.
- Mobile usage with smartphones: Using FIDO and NFC, you can also securely access your accounts on Android and iPhone smartphones.
- Encrypt data and emails: Encrypt your emails with GnuPG, OpenPGP, S/MIME, Thunderbird or Outlook. Encrypt entire hard drives using TrueCrypt/VeraCrypt, LUKS or individual files using GnuPG. Your private keys are securely stored in Nitrokey and cannot be exported/stolen.
For companies - protection against hackers and industrial espionage
- Passwordless logon to Windows 10 computers: Employees will be able to log in to their Windows 10 Pro computers managed by Azure Active Directory without passwords. All that is required is a Nitrokey 3.
- Passwordless login to your own enterprise systems: Replace your password policy, unauthorized password slips and costly password resets with passwordless login with the Nitrokey 3. Security and acceptance through simplicity. We are happy to advise you on integration.
For IT administrators and security experts - protect critical infrastructure
- Administering servers securely with SSH: Always have your SSH key securely with you in Nitrokey. Your key is PIN protected and cannot be exported/stolen from the Nitrokey. This eliminates the insecure and annoying synchronization of key files on client systems.
- Protect Internet of Things (IoT) and own products: Protect your own hardware products by integrating Nitrokey. Ideal for remote maintenance and ensuring product authenticity.
- Store cryptographic keys securely: Store cryptographic keys and certificates securely in Nitrokey, preventing their theft.
- Protect computer BIOS integrity: Using the Nitrokey and Measured Boot, the integrity of the computer BIOS/firmware is verified. The colored LED of the Nitrokey signals whether the BIOS has integrity (green) or whether tampering has been detected (red). Compatible e.g. with NitroPads.
Functions
- FIDO U2F, FIDO2 for passwordless login: FIDO sets new standards in easy usability and thus achieves high acceptance. FIDO reliably protects your accounts against password theft and phishing.
- Disabled passwords to protect accounts against identity theft: Protect your accounts against identity theft. One-time passwords are generated in Nitrokey and serve as a second authentication factor for logins (in addition to your normal password). Thus, your accounts remain secure even if your password is stolen.
- Secure cryptographic key storage: Store your private keys for encrypting emails, hard drives or individual files securely in Nitrokey. This way they are protected against loss, theft and computer viruses and are always with you. Key backups protect against loss.
- Password Manager: Store your passwords securely encrypted in the integrated password manager. This way you always have your passwords with you and they remain protected even if you lose your Nitrokey.
- Integrity Check / Tamper Detection: Verify the integrity from the computer BIOS using Verified Boot. The Nitrokey's colored LED indicates whether the BIOS has integrity (green) or tampering has been detected (red). Supported computers require a BIOS based on Coreboot and Heads such as the NitroPad.
Security Technology
The Nitrokey 3 is based on a novel security architecture:
- All firmware is developed in the memory-safe programming language Rust. This avoids potentially security-critical memory errors.
-
The firmware is based on the framework Trussed developed in Rust, which is designed for security-critical embedded systems and developed in cooperation with our partner SoloKeys. Among other things, Trussed implements cryptographic operations. Of course, the code is published as open source.
The hardware is based on the LPC55S6x microprocessor, which has numerous security features, such as Secure Boot, ARM TrustZone, Physical Unclonable Functions (PUF).Update: The hardware is based on different microprocessors that support Secure Boot and other security features.- Additionally, a Secure Element, quasi a smart card, is used for the cryptographic memory. This has been security-certified up to the operating system level according to Common Criteria EAL 6+ and thus also meets high security requirements. Due to the power requirement, the secure element can only be used via USB but not via NFC.
- As with all Nitrokey developments, Nitrokey 3 is open source, so the secure implementation can be reviewed by anyone.
To receive the latest status updates on your Nitrokey 3 order by email, sign up for our newsletter. This is required so that we may contact you by email.
Status Update, 6/14/2022
From now on we will publish future status updates regarding Nitrokey 3 in our blog instead of here.
Status Update, 5/13/2022
The circuit boards of the Nitrokey 3A Mini could not be fully assembled yet, because a passive component is missing. This should arrive next week, which means that the first series production can begin, which we will then test.
The firmware development for the nRF52 or Nitrokey 3A Mini has reached alpha status, i.e. is functionally equivalent to the LPC55S variant (FIDO2). Now the primary focus is on debugging and stabilization.
The next production slot for the Nitrokey 3A NFC unfortunately could not be fixed yet; we are working on it and will keep you informed. However, since the critical component is already in stock (LPC55S), we are optimistic that it will start soon.
Status Update, 4/13/2022
Currently all Nitrokey 3 support FIDO2 functions only. We have released some firmware updates in the last months that fix most of the issues. To update your Nitrokey 3, please follow the instructions. An overview of available firmware updates can be found here.
The delivery of the Nitrokey 3A NFC and the Nitrokey 3C NFC of the first production batch has been completed. Unfortunately, we were not able to fix the technical problems on all devices according to our quality standards, which is why the first production batch turned out to be smaller than expected. Therefore, some orders are slipping into the second batch. Affected customers have been informed personally by e-mail.
We have received the PCBs for the Nitrokey 3A Mini. Now the assembly of the first PCBs will be done soon. After that, there are further steps to be done, such as checking compatibility with the package, flashing, assembly and extensive quality control. The Nitrokey 3A Mini can then be shipped, probably at the end of Q2 or beginning of Q3 2022.
We have received another 1000 pcs. LPC55S microprocessors. With this, we will produce another batch of Nitrokey 3A NFC. Production has been ordered and is expected to take 6-8 weeks. Minor improvements to the hardware layout have already been incorporated to simplify assembly and improve NFC performance.
Porting to the new microprocessor is not yet complete, so the Nitrokey 3A NFC is not expected to be available from stock in large quantities until Q3 2022.
For the Nitrokey 3C NFC, we have decided to develop a new casing. This will provide greater robustness and allow for faster production. The development time of the casing is currently difficult to estimate. Therefore, the production schedule for the Nitrokey 3C NFC has been postponed to Q4 2022. Pre-orderers of the Nitrokey 3C NFC who would like to change their order to the Nitrokey 3A NFC, please email us to "shop at nitrokey dot com".
As soon as there is a change in the current estimate, we will inform you here immediately.
Status Update, 2/5/2022
Unfortunately, some of the shipped Nitrokey 3A NFC (with USB-A connector) have a technical error that results in weak NFC performance. If you have problems using NFC with your Nitrokey 3A NFC, we offer you a free device exchange. Therefore, please send us your Nitrokey 3A NFC and state your order number. The Nitrokey 3C NFC (with USB-C connector) is not affected by this.
Accordingly, the complete delivery of the first production batch is unfortunately still delayed.
Porting to the new microprocessor is progressing and we plan to complete by the end of the month. Once porting is complete, we plan to produce additional Nitrokey 3A NFC and Nitrokey 3A Mini. These models are then expected to be available in Q2 in sufficient numbers to service all pre-orders and also to fulfill new orders immediately.
More Nitrokey 3C NFC (with USB-C connector) will be delivered in the next few weeks. A new production of this model is planned for the 3rd quarter.
Status Update, 11/25/2021
The delivery of the Nitrokey 3A NFC has started. Furthermore, the delivery of the Nitrokey 3C NFC is progressing. All customers who have subscribed to the newsletter have been informed about their expected delivery status or production batch. The production and delivery of the many pre-orders takes time and our team is working at full speed to ship as many orders as possible every day.
Status Update, 10/18/2021
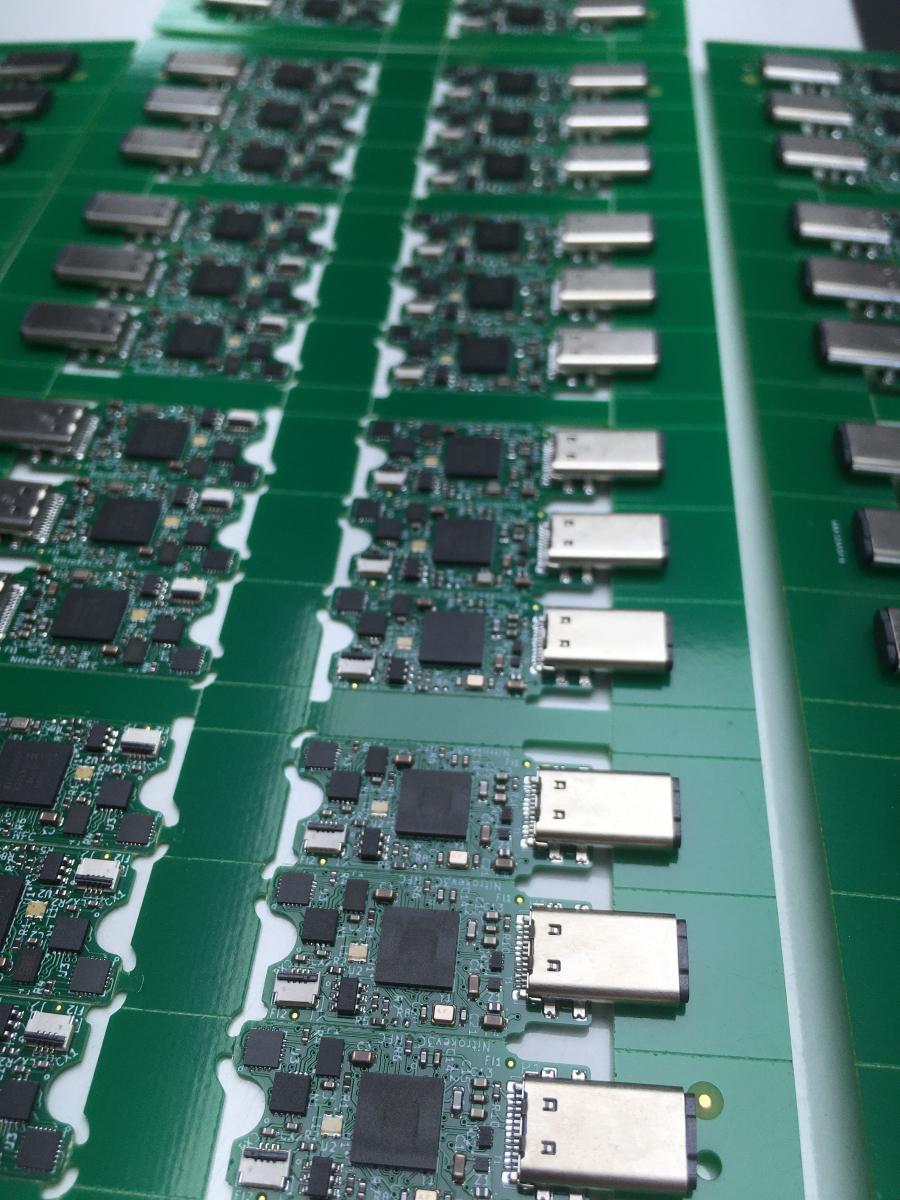
The first Nitrokey 3C NFC were produced and shipped. Production and delivery of all pre-orders is expected to take several weeks. All pre-orderers will be informed via email as soon as their Nitrokeys have been shipped. Pre-orderers who will only be served from the next production batch will be informed via email in the next few weeks.
Status Update, 10/8/2021
Important: The batch of both NFC models now in production is already sold out. All new orders of a Nitrokey 3A NFC and Nitrokey 3C NFC will be served from the next production batch. Due to the electronics shortage, porting to the nRF52 must be completed for this. We expect delivery later this year and will post regular status updates here. Customers who ordered already will be informed in the next days and weeks from which production batch they will be served resp. when they will be delivered.
Nitrokey 3C NFC: The electronics are completely procured and produced. Also, the new cases have been produced and are now being printed. Next week we will begin flashing the firmware, installing Nitrokeys into the cases, testing and shipping. Production and delivery of all pre-orders is expected to take a few weeks.
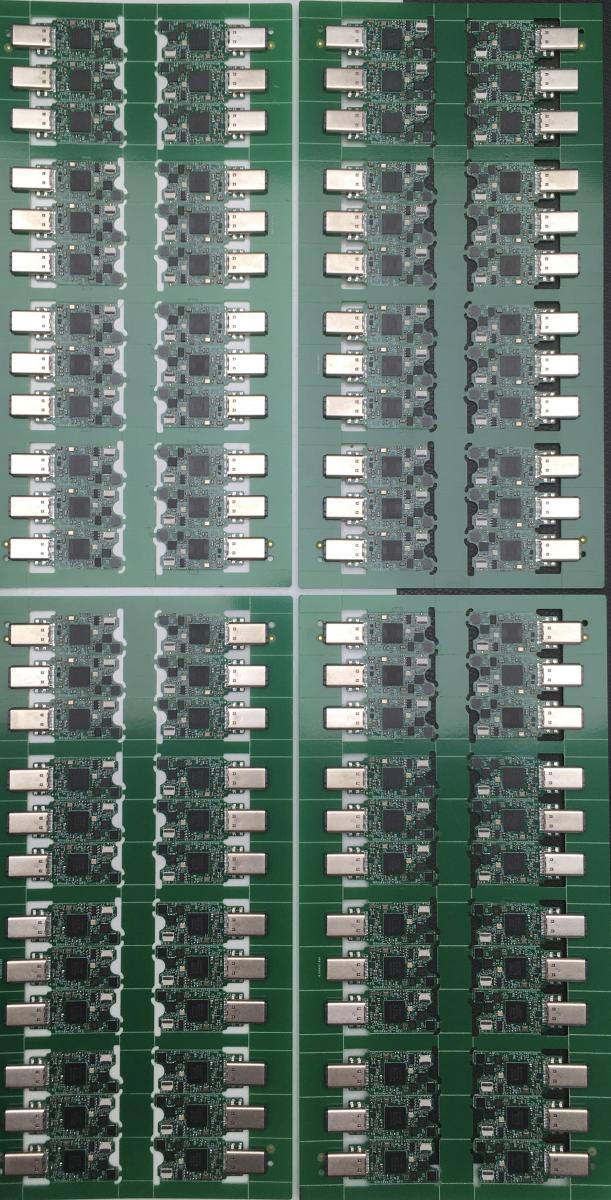

Nitrokey 3A NFC: For the USB-A model, the PCBs, electronics and enclosures are fully sourced. However, we fortunately unexpectedly found a way to further improve the NFC performance. To do this, we had to do another electronics change and test cycle. Unfortunately, this will delay the delivery by probably 2-4 weeks.
Nitrokey 3A Mini: Electronics and case development is complete. Firmware porting (to the nRF52) is still in progress. We plan to produce and ship in the next few weeks. The quantity should be enough to serve all pre-orders and fill our warehouse for the next weeks and months.
Status Update, 8/25/2021
- The development of the Nitrokey 3C NFC casing has been completed.
- Planned delivery date for the PCBs is week 40. The subsequent assembly is planned with a few days.
Status Update, 8/11/2021
- Development of the Nitrokey 3A Mini and Nitrokey 3C NFC enclosures has made significant progress. We plan to complete the enclosure development concurrently with the availability of the assembled electronics.
- The required NFC chips have been delivered and tested successfully. Barring any further supply bottlenecks, the electronics will be assembled shortly.
- In order to achieve the best possible availability despite the global electronics shortage, we will equip the Nitrokey 3 with different microprocessors. Users will not notice this internal difference, but for us it means more effort. Therefore we had to redesign the electronics of the NK3A Mini using the nRF52. We expect the electronics samples next week. We have already got the firmware working on the nRF52 but the porting is not finished yet.
We plan to start shipping the Nitrokey 3A NFC and 3C NFC first. The Nitrokey 3A Mini is expected to start a little later. We are now waiting for our contract manufacturer to assemble it. We can't give a specific delivery date yet but it shouldn't be long.
Status Update, 6/11/2021
In the last months and weeks the development of the Nitrokey 3 has made significant progress. Nevertheless, its delivery will unfortunately have to be delayed, especially due to lack of electronics.
We have achieved:
- The electronics development is finished and the electronics works stable.
- The firmware has FIDO2, which can be used via USB and NFC.
In work at the moment is:
- Electronics procurement and production has started
- Firmware development of one-time passwords (OTP) and the password safe.
- Porting of firmware to the nRF52 microprocessor. This is important to be able to avoid future supply shortages that we are facing due to the global electronics shortage.
The delivery of the Nitrokey 3 depends on:
- We are waiting for an electronics component to arrive no later than July.
- Completion of the case development
It is anticipated that the Nitrokey 3 will ship in the next few weeks or during the summer. We apologize for the delay and ask for your understanding.
Comments
Pages
Add new comment