Milestone for Nitrokey 3 Achieved: OpenPGP Card, One-Time Passwords and USB-C Availability!

Today, we are excited to announce the official release of the Nitrokey 3 firmware version 1.4.0. This is a big achievement for us, as the new firmware enables long-awaited features that will further improve privacy, security and ease of use for our users. Moreover, the production of the Nitrokey 3C NFC model has been sped up exponentially lately: we’re shipping hundreds of units every week and we expect to have all pre-orders shipped by the end of next week. From then on all Nitrokey 3 models will be on stock and available to order in our online shop. We would like to thank our users for their patience, hoping the result will be worth the wait. Now, let’s take a closer look at the new features that come with firmware 1.4.0!
OpenPGP Card
Arguably the most awaited feature for Nitrokey 3 is the OpenPGP Card. It’s a smart card that is often used for OpenPGP (Pretty Good Privacy) and GnuPG (GPG) to encrypt user data and e-mails. OpenPGP Card can also be used for arbitrary encryption, signing, and authentication use cases such as secure and convenient SSH logins. The new firmware now allows you to securely store your private keys on a Nitrokey 3 and use them on the go. For now your keys will be stored encrypted in flash and not in the secure element yet. Security does not sacrifice transparency: as usual, the new firmware is released under a fully open source license, allowing users to inspect the code and modifying it; something that sets Nitrokey apart from competitors.
One-Time Passwords (OTP)
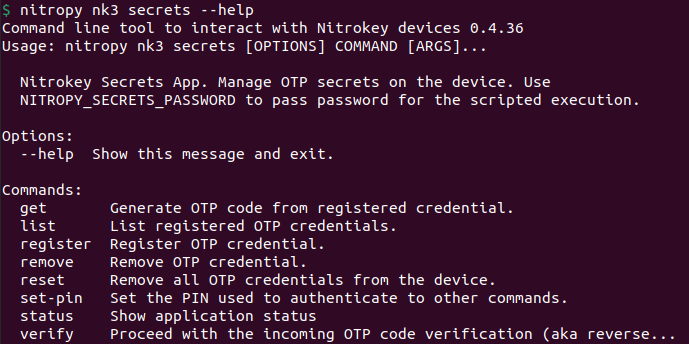
One Time Passwords (OTP) are supported alongside the OpenPGP Card. It enables Nitrokey 3 to generate one-time passwords that, when enabled, during login will be requested from the user as a two-factor authentication (2FA) method after they entered their password. This approach combines something you know (the password) with something you have (the device generating the OTP), making you less vulnerable to password phishing attacks. For the time being, One Time Passwords can be generated through the nitropy command-line tool, but we have news in this regard as well. Read on…
Graphical User Interface: Nitrokey App 2
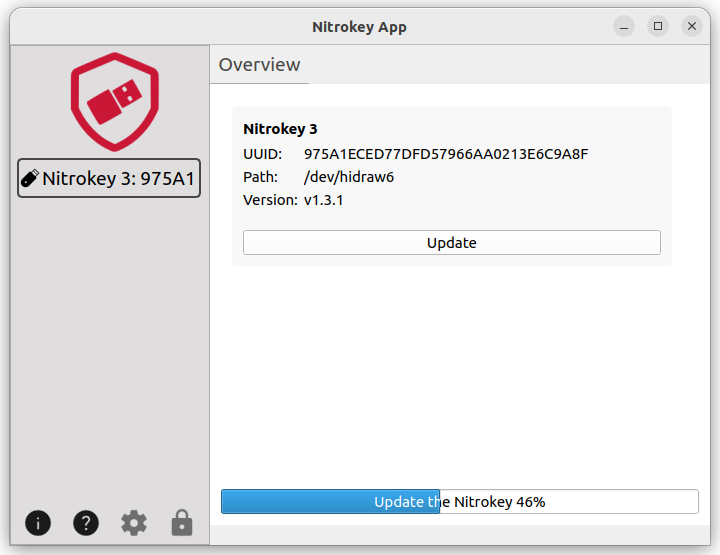
We recently released the Nitrokey App 2! Newly developed from scratch in Python, the app takes advantage of the pynitrokey library to feature an intuitive design to manage all Nitrokey 3 devices. Nitrokey App 2 is currently available through an MSI installer for Windows and a binary file for Linux, while a Flatpak version and macOS support are being worked on. It can already be used to update the Nitrokey 3 firmware and support for one-time passwords is expected to become available soon.
What to Expect in the Future
Our team is already working on new functionalities, such as adding a password store into the Nitrokey 3, support for the popular password manager KeePassXC, PIV to allow passwordless logins for enterprise Windows users, integration with NitroPad resp. HEADS for measured boot, SE050 Secure Element integration, and to encrypt and sign data in web browsers with Nitrokey 3 and without additional client software. Stay tuned!
By the way: If you want to be informed more frequently about news and development progress, follow our blog.
Comments
- Once the SE implementation is in place, will the users need to do anything to move them or will that all be taken care of via the update and...
- Will the users be better off factory resetting the keys and letting the NK regenerate them, or is will the automated process (if it will exist) be sufficient enough.
- What the security implications of the keys residing in flash and/or what security measures have been taken to ensure the security of the keys for now.
Mainly asking to figure out how much trust can be put into the NK3 with the firmware in its current state. I'm assuming that with the keys being stored in the flash, the key isn't as resistant to physical tampering. Thank you, and all the bestAdd new comment